Understanding XSS Attacks
Complete breakdown of Cross-Site Scripting and modern defense mechanisms.
Insights, tutorials, and discoveries from my cybersecurity journey
Complete breakdown of Cross-Site Scripting and modern defense mechanisms.
 CULTURE
CULTURE
White hat, Black hat, Grey hat - demystifying the colors of cybersecurity.
 DEEP_DIVE
DEEP_DIVE
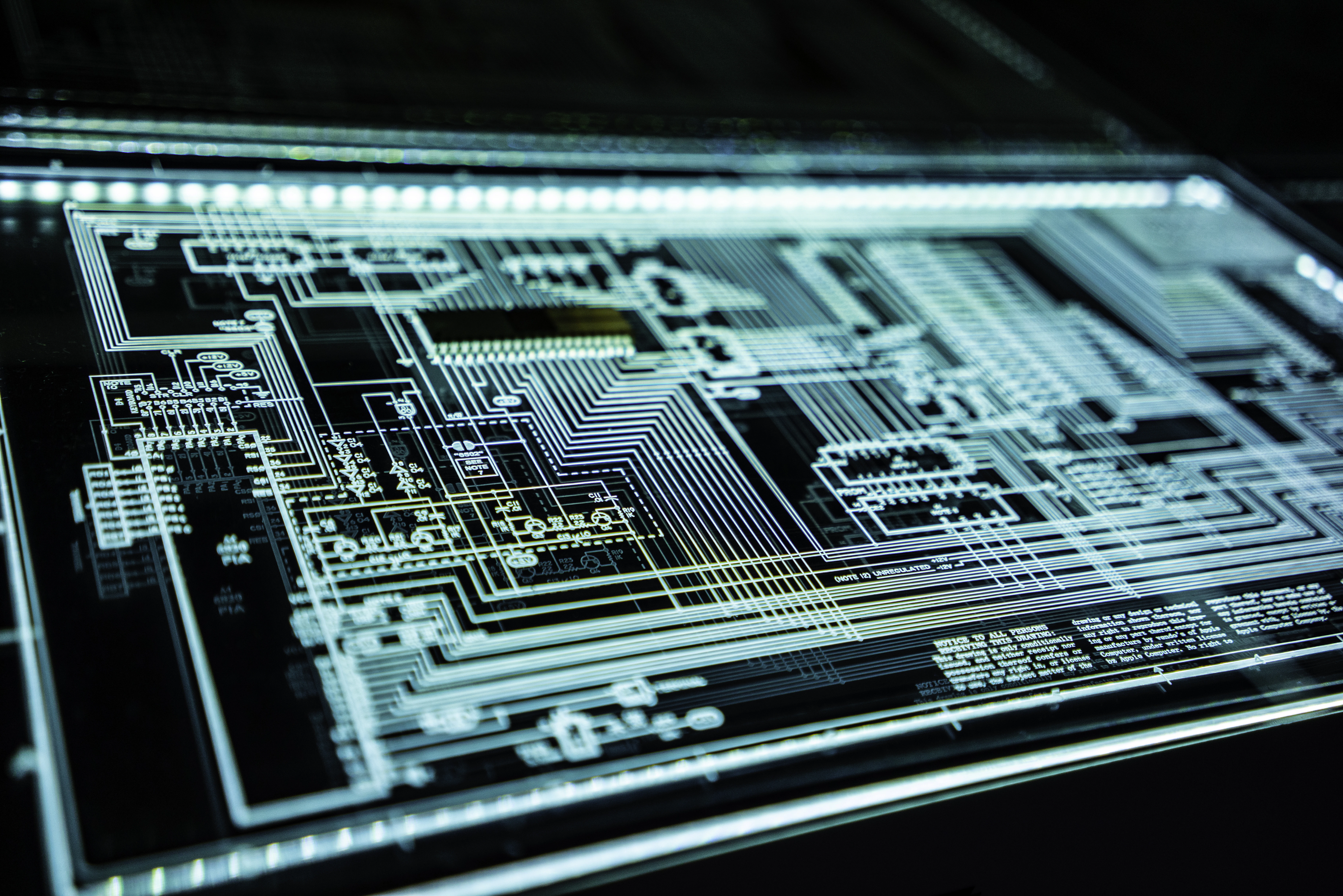
Analyzing the architecture of a secure web project: CSP, Headers, and Encryption.
 FUTURE
FUTURE
How intelligent agents are reshaping the way we work and code.
 PENTEST
PENTEST
Finding and fixing SQL Injection and XSS in a standard LAMP stack application.
 CPP_DEV
CPP_DEV
Building robust console applications with file handling and OOP principles.
A local-first, zero-knowledge password manager built for privacy enthusiasts.
 AI_TOOLS
AI_TOOLS
Optimizing your workflow with the latest artificial intelligence solutions.
 MALWARE
MALWARE
Educational analysis of GhostKey - understanding endpoint surveillance and defense.